A while back, someone on Twitter mentioned me in a tweet asking, “what are the top 5 things you think admins need to be doing for Office 365 Security and Compliance?” I responded via Twitter and some dialog ensued. However, Twitter obviously has limitations to the length of response and going back and looking something up like this, or finding it later isn’t always easy. So, I decided to turn it into a blog post (and finally got around to writing it)! However, if you do want to go back and read the Twitter conversation, here it is.
TL;DR
So, what are my top five? First a clarification, I create this list based on the assumption you have Office 365 E3 without any additional add-ons. In my experience, this is the plan that most people tend to go with. If you do have Microsoft 365 E3, Office 365 E5 or Enterprise Mobility + Security (EMS), this list still applies, but there are also some additional features you’ll have access to that you can take advantage of when it comes to compliance and security.
If you want to know more about why I choose these and further details around each one, I’ll dive into all the details after the bullet list.
- Enable the Unified Audit Log – I think it’s crazy that this is actually disabled by default…seriously, go turn it on now.
- Enable and take advantage of multifactor authentication (MFA) – Do it in Office 365, but also use this on any other site/service that supports it. This goes a long way toward securing your account on any site.
- Purchase EMS or Office 365 E5 for your Office 365 Admins and enable Privileged Identity Management (PIM) – I know it requires purchasing something, but it’s worth it and prevents your admins from having standing admin access to Office 365
- Actually, Plan and Think about how/where you allow external sharing – This shouldn’t be a blanket enable/disable, enable where is make sense, disable where need. In some cases enabling it can make your environment more secure.
- Configure Data Loss Prevention to protect sensitive content – If you have Office 365 E3 or E5 you have the license for it, just
go configure it. - Yes, you counted right, this is number 6 in my top five. As mentioned the top five can all be done without purchasing anything, with the exception of number 3 which is just a small number of additional licenses for admins. This is probably a much larger purchase and investment. Purchase EMS E3 or EMS E5 for ALL your users.
Diving into the Details of each of the top 5 6 Office 365 Security and Compliance Considerations
Ok, you got the overview, here are all the details of why I chose the 6 Office 365 features and how you can leverage them to better secure your Office 365 environment.
Enable the Unified Audit Log
It was between the Unified Audit Log and MFA for number 1. Honestly, these should both be a no brainer, when it comes to security and compliance. I chose the audit log as number 1 simply because it doesn’t require any interaction with the end-users. To start, you just turn it on. I actually can’t believe this isn’t enabled by default in Office 365 tenants. There is probably some regulatory reason it isn’t on by default.
So, how do you enable it? Navigate over to the “old” Security and Compliance Center (https://protection.office.com/) in Office 365, expand out “Search” and click on “Audit Log Search”. If it’s not enabled you’ll get a bar across the top letting you know it’s disabled and providing the link to enable it. If it is enabled? No bar and you’ll be able to start search the log. Once you do enable it, it can take up to 24 hours to start seeing data, but after that you can find anything usually within a minute or two of it occurring.
Anyways, this is in the security and compliance center and again, in my option, it should be enabled right away. This logs nearly everything that goes on in your Office 365 tenant and can be invaluable when it comes to tracking down a security or compliance issue. It logs deletions for files and emails. Will audit who logs in, from where and what time. It shows files that are shared external and emails that are forwarded. It is what will allow you to go back after an event and find out what really happened.
Oh, and if you need to know in real-time? You can set alerts on the audit log. Say every time someone creates a new site collection in SharePoint, or sets up a new mail forwarding rule. The unified audit log also helps you be proactive in catching specific events as soon as they happen.
One last thing to note, as you might imagine, storing this much audit information can take quite a bit of storage. Especially when you take into account the amount of Office 365 tenants there are. As a result, Microsoft current only stores the past 90 days of this audit data. As it stands right now, if you want to keep it longer, you’ll have to manually download/export it and save it somewhere else. There were plans about 12 months ago to provide the ability for you to store it for longer periods of time in your own Azure tenant, but that seems to have stalled out. Who knows, maybe we’ll see it resurrect itself sometime down the road.
Use Multi-Factor Authentication (MFA)
Multi-Factor Authentication (or MFA) is another one of those things you should enable right away. In fact, in certain scenarios, Microsoft is even starting to require it. Examples are:
- The Security Defaults that are coming in February of 2020
- The Common Conditional Access Policies
- A requirement for all CSP/Microsoft 365 partners to have MFA enable to continue with their partner access
I really like the fact that Microsoft is starting to make this a requirement. There are so many instances, where simply having MFA enabled would have prevented attack and data leaks. If you don’t have this enabled already, do it before you read any further. Here is the link to go enable the “Security Defaults” if you want a quick and easy way to enable it.
If you want to take it a step further, you can also do some really neat things with conditional access policies around when you require MFA (i.e., maybe you don’t want to require MFA when users are known to be in your office and on the local network).
Privileged Identity Management (PIM)
Privileged Identity Management. I’ll start this out by saying this is an E5 feature. However, this doesn’t require you to get E5 for all your users. I would recommend E5 for admins just for privileged identity management for those admins.
For those coming from an on-premises world that are used to having to accounts 1) your “normal” account – day-to-day activities 2) your “admin” account – managing servers and server products; this enables to you roll two accounts into one (and a single E5 license is cheaper than two E3 licenses). You now have a single, Microsoft 365 account that is a “normal” user by default. However, with privilege identity management enabled, you can elevate this account to an admin account for a limited period of time, take care of the admin activities, and then it will automatically revert back to a normal account.
External Sharing
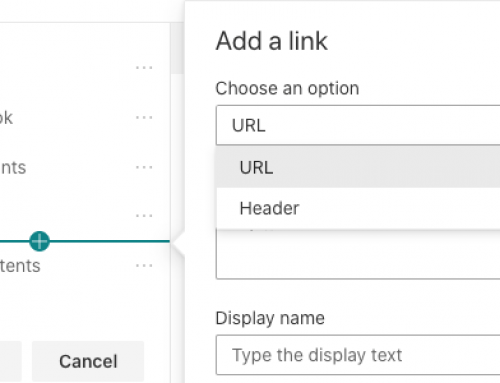
Put some thought in external sharing. Definitely don’t just disable it, it’s a powerful and very useful feature of Office 365 and more specifically SharePoint Online. However, you may want to put some controls around it. Maybe you do want it disabled on sites like Human Resources, Finance, and your Executive Site. It’s possible you may not want to allow anonymous sharing, but force people to login, and even limit them to logging in using only the email address the file was shared with.
You can also force expiration policies for when anonymous links expire if you do allow them. Or set up alerts in Cloud App Security (EMS E5) to alert you of stale externally shared content so you can go remove the sharing permissions.
You need to be aware of and put some thought into how your organization will handle external sharing of content. It’s not just an on/off switch or something to ignore.
Data Loss Prevention (DLP)
Configure Data Loss Prevention. This goes hand in hand with external sharing above. Just because you have external sharing enabled doesn’t mean you can’t enable controls around what content can be shared.
Above we discussed sharing content and limiting that sharing at a site level. DLP takes this even a little further. Now you allow sharing on a site, but use data loss prevention to prevent financial information, social security numbers, personal information, etc from being shared. DLP in Office 365 uses intelligence to automatically detect sensitive information in SharePoint, Outlook/Exchange, Teams, and OneDrive to prevent this sensitive information from being shared.
Microsoft has a TON of sensitive information types included in Office 365 by default. However, they also let you define your own sensitive information types. Say maybe you have customer account numbers that you don’t want shared or some other internal information that you can define and you wish to protect with DLP. Microsoft gives you the ability to define those types and add them to DLP.
Enterprise Mobility + Security (EMS)
EMS 3 or EMS 5 in my opinion is becoming a must-have. I get it, not everyone can take on the additional $8 – $16/month/user. But if you can, seriously, go purchase it. EMS E3 is usually adequate for more organizations. And for the extra $8/user/month you can a ton of extra security features.
EMS E3 allows you to:
- Define conditional access policies
- Manage corporate devices
- Manage corporate data on personal devices (BYOD)
- Leverage Azure AD Premium features for guests (5:1 ratios of guests to licensed users)
- Advanced Threat Analytics
- Additional Security reporting
In my opinion, the EMS licenses are worth every cent (assuming you enable take advantage of the include services) and allow you to take the security of your environment and your data to the next level.